Adding People to Groups in OpenLDAP using Apache Directory Studio
[ This post is part of my ongoing instructional series on setting up some baseline IT infrastructure for the fictional startup Shoestring Lab. Shoestring has committed to using Open Source wherever possible. Shoestring Lab has standardized on Ubuntu for its server and desktop/laptop computer systems.
Today's lesson
Part of your job is managing user access to various internal computer resources. This task involves adding people to groups in OpenLDAP.]
Now that you have people and groups entered into your OpenLDAP service, you need to associate the two so you can provide granular control over access to your system services. You are going to add a person to the users group.
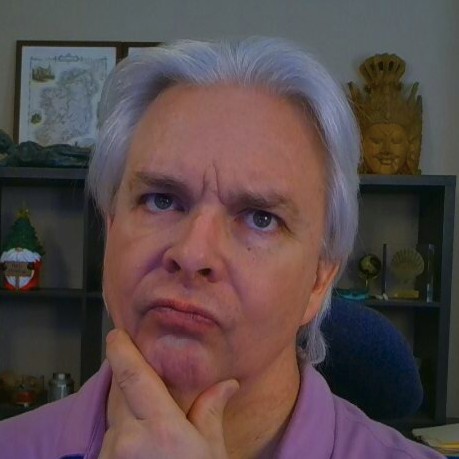
Open Apache DS. Open the connection to your OpenLDAP service. Open the root DSE until you see the entries for ou=people and ou=groups. Open ou=people and select the person you created previously. You will notice at the top, just under the tab and over the column title "Attribute Description", there is a line of text that starts: DN: and runs under the adjacent entry. Select that area, right click and select "Select All", then right click again and select "Copy".
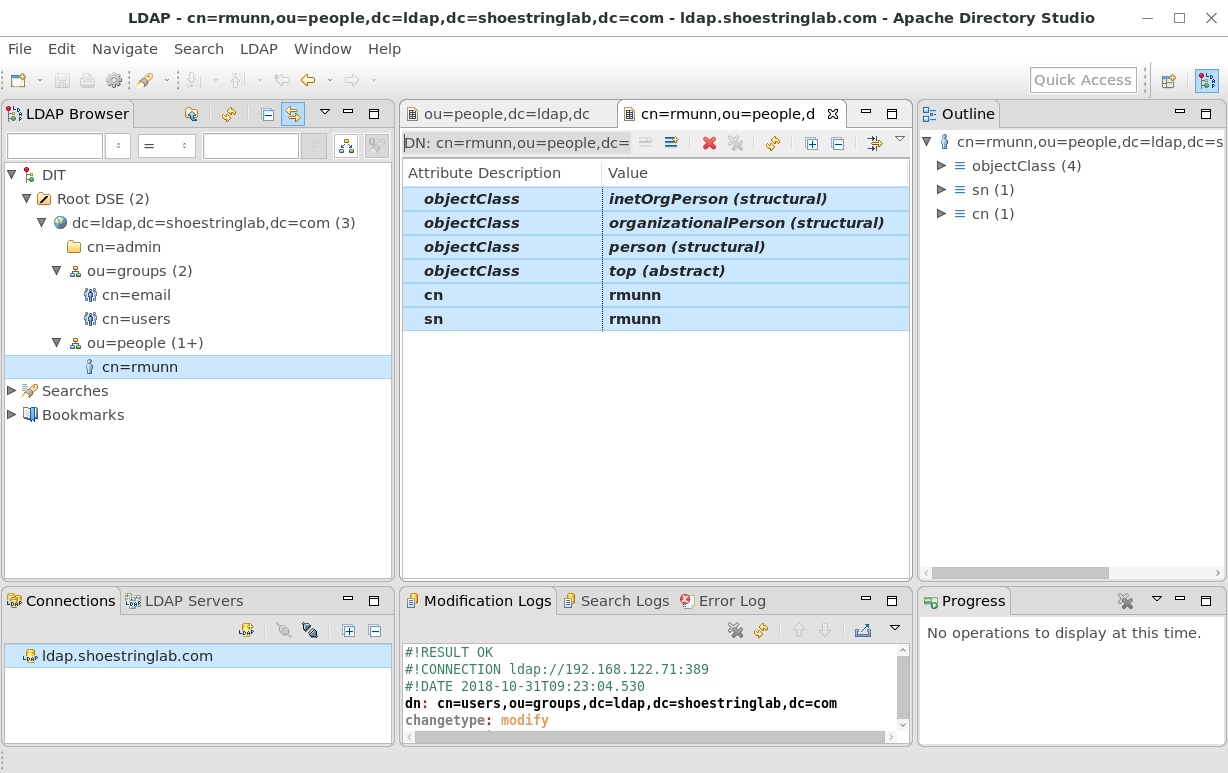
Next, open ou=groups and select the cn=users entry. Select the text box at the right of the uniqueMember value.
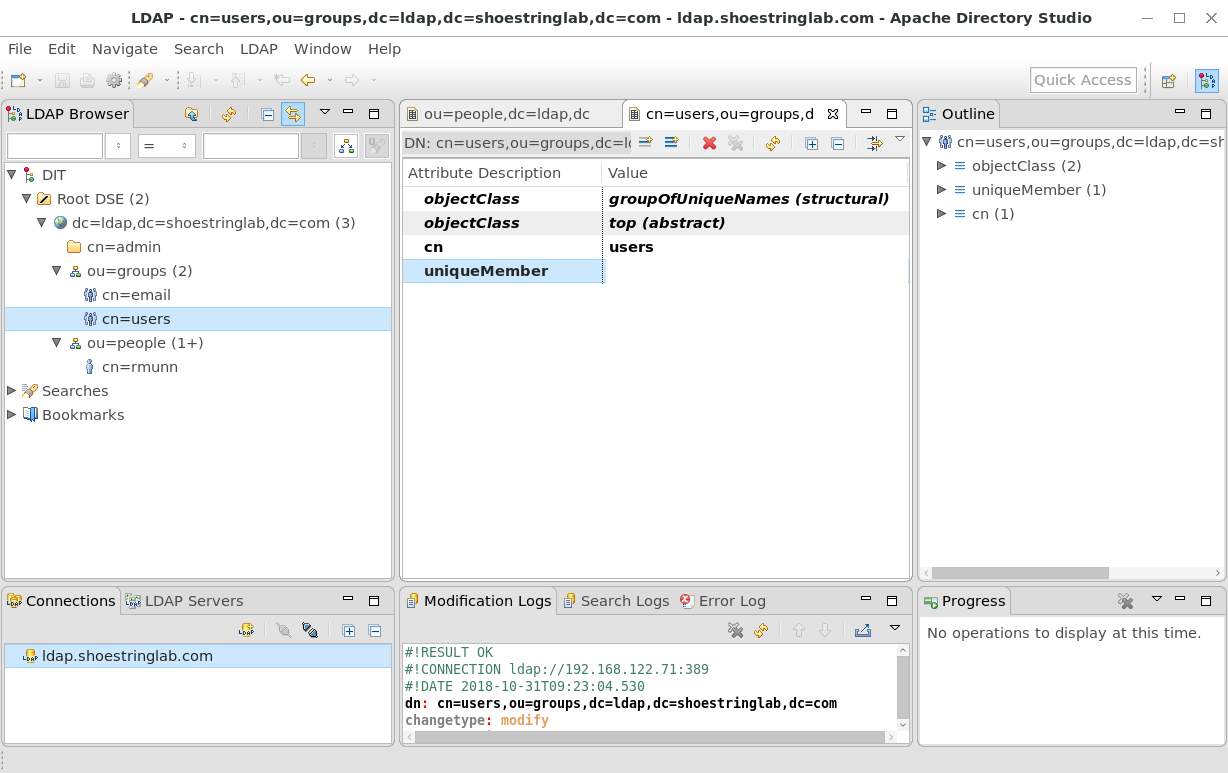
Paste the copied text from the people entry into this value box. Remove the leading "DN: " text so the entry starts with cn=<username>.
To add another uniqueMember entry, right click on the current uniqueMember entry and select "New Entry".
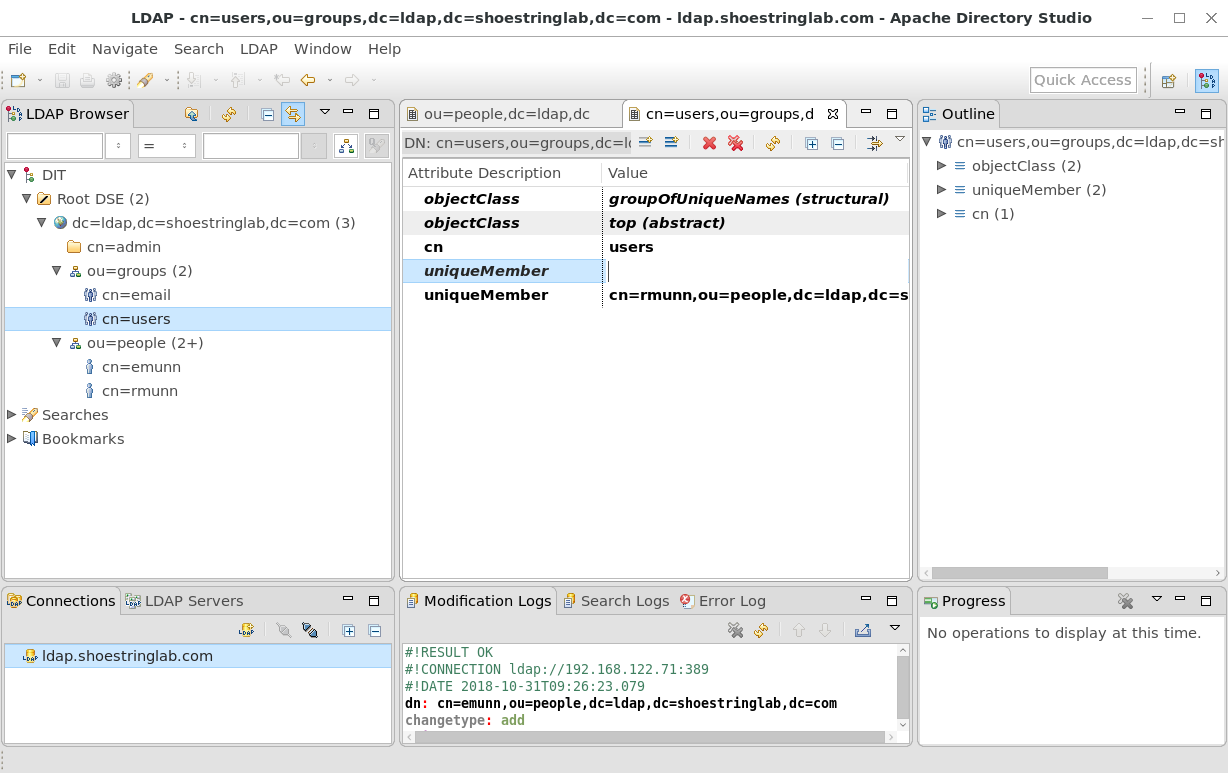
Repeat the process for adding a person entry as a uniqueMember of the group, or just enter the value manually. You should see the pattern the the person entries now.
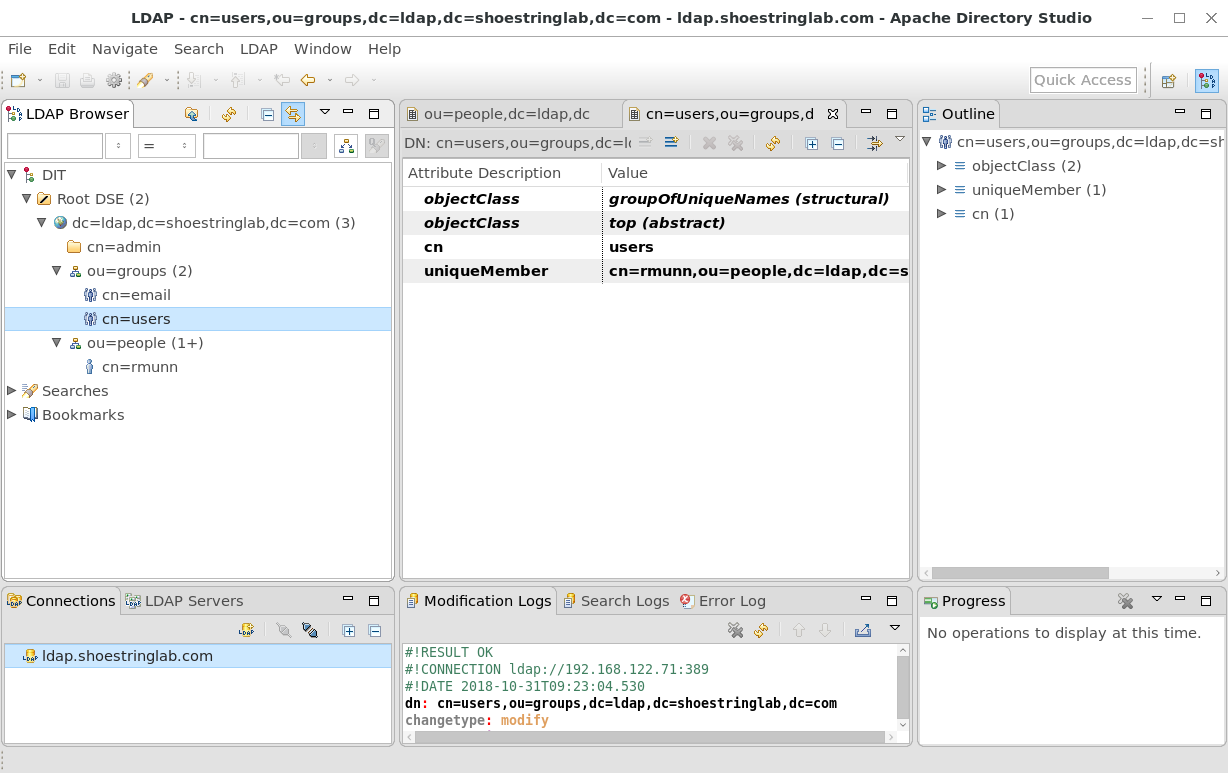
Using this technique, network services can query the OpenLDAP service using a filter on the users group to see whether a given user has been granted general user access.